Arming the acquirer to forge a decisive edge
The Core Problem: Forced Dependency and the High Cost of Waiting
It is a familiar and frustrating story: a multi-million-dollar weapon system that is key to a unit’s survival is rendered inert by a problem the unit has the skills to fix—but not the permission or knowledge to do so. Marines, trained to be self-sufficient, are reduced to customers waiting for a service call. On the battlespace, this waiting robs them of what makes them dangerous: their initiative, adaptability, and the ability to keep fighting when everything goes wrong.
The Mandate: Acquisition as a Warfighting Function
To eliminate this scenario of forced waiting and dependency, a new mandate from the Secretary of War gets directly to the point. This urgency is a direct response to a rapidly shifting global security landscape, where the resurgence of near-peer competition and the pacing threat of technologically advanced adversaries means victory will be decided by speed, resilience, and adaptability. The directive has fundamentally reshaped the landscape of military acquisition, redoubling focus on a single, uncompromising objective: delivering a decisive edge to the war-fighter at the speed of relevance. The directive, “Transforming the Defense Acquisition System into the Warfighting Acquisition System,” is more than a change in name; it is a seismic shift in philosophy. It declares that acquisition is not a support function, but a war-fighting function, critical to deterring our adversaries and winning the Nation’s battles. For the Marine Corps, this means treating an acquisition contract as a weapon. It requires arming the acquisition workforce, empowering the maintainer, and unifying our efforts for a decisive edge.
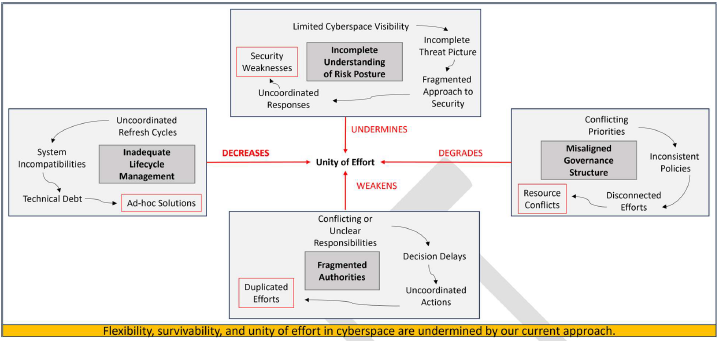
This transformation directly addresses the systemic challenges the Secretary of War identified that have historically hampered progress. For the Marine in the field, these challenges have manifested in tangible, mission-impacting ways: delays in fielding urgently needed capabilities, extended downtime for critical equipment, and a costly over-reliance on contractor support that cannot keep pace with operational tempo.

The core principles of the new War-fighting Acquisition System are simple and direct: instill a warrior ethos in the acquisition workforce, inject a relentless focus on speed and urgency, and empower those responsible for delivery to make and own their decisions. Every process, board, and review must now justify its existence by proving it directly supports accelerating capability to the FMF. We will no longer treat barriers in contracting and acquisitions as administrative hurdles but as a direct operational risk to mission success.
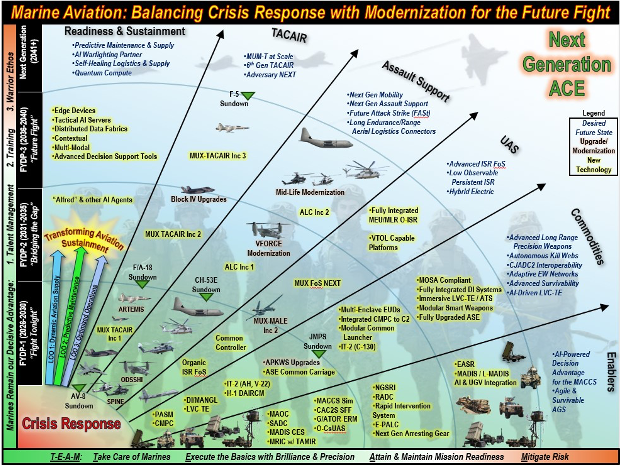
Marine Corps Systems Command’s Strategic Response: Equipping an Unrivaled Fleet
Answering this call to treat acquisition as a warfighting function, Marine Corps Systems Command unveiled its 2025–2032 strategic plan serving as the command’s roadmap. In the plan’s opening message, BGen Tamara L. Campbell, Commander of Marine Corps Systems Command, outlines a vision for “Equipping an unrivaled, future-focused Fleet Marine Force, powered by a dedicated acquisition workforce.” She further states, “The future threat is ever evolving, and we must be prepared to modernize our approach and processes to meet and defeat that threat.” This modernization enables the continuous adaptation of our warfighting capabilities to ensure Marines can forge an unfair fight and win. Marine Corps Systems Command is focusing on key areas of program management, process improvement, partnerships, and talent management to accelerate the delivery of lethal, agile, and ready capabilities. For Marine Corps Systems Command, the Secretary of War’s mandate is not just a new requirement to be met but a confirmation of the path it is already on—a path dedicated to ensuring that every acquisition decision directly contributes to combat power.
The Ownership Imperative: Forging Self-Sufficiency
Putting this warfighting mandate into action, Marine Corps Systems Command is focusing on its approach to contracting, intellectual property, and system maintenance. For a Marine in a contested environment, the legal jargon of a contract is a distant concept until the way the contract was written impacts mission success and survival. Marine Corps Systems Command’s new Product Support Strategy policy addresses this reality, which transforms acquisition strategy into a direct lever of combat power by ensuring the Marine Corps truly owns the systems it fields. Strengthening contractual rights in the acquisition of a system means a Marine can make necessary repairs or modifications to the system to sustain combat power instead of relying on a contractor to do so at additional cost and/or delay.
To make this a reality, the era of accepting unnecessary “vendor lock”—where the Marine Corps is denied the technical data and intellectual property rights to repair its own equipment—must end. While we respect our industry partners’ need to protect their commercial interests, dependency on a sole-source vendor creates a critical warfighting vulnerability that we can no longer accept. Doing so means navigating a complex legislative environment where established intellectual property laws, designed to protect innovation, can inadvertently hinder battlefield readiness. This necessary shift has, predictably, sparked debate, but the acquisition and sustainment communities will need to continue to drive for expanded data rights and technical data packages required to leverage advanced manufacturing, ensuring our systems remain lethal and sustainable in any environment.
… the Marine Corps is arming its acquisition workforce with the authority, tools, and analytical capabilities …
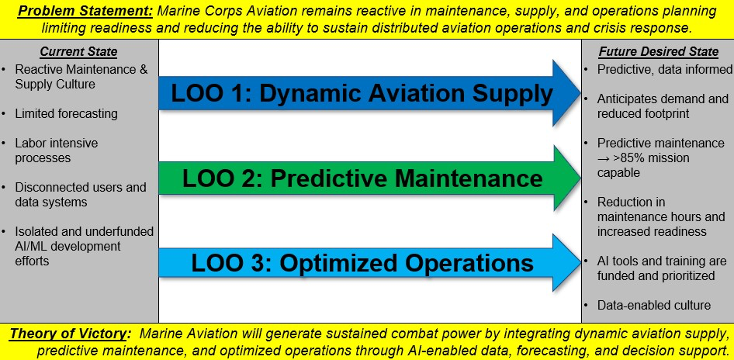
Marine Corps Systems Command’s Product Support Strategy order also makes it clear that failing to secure intellectual property and data rights is no longer an acceptable risk. The order is a direct response to the battlefield costs of ignoring this risk: degraded readiness, atrophy of organic maintenance skills, uncontrolled cost growth, and reduced lethality. The policy mandates that we must prioritize the “maximum integration of organic supply and maintenance capabilities while leveraging the Joint Logistics Enterprise’s capabilities, where appropriate,” shifting the focus from slow, outsourced repairs to swift, organic sustainment performed by uniformed Marines at the point of need. This reinforces the warfighting ethos of self-sufficiency and ensures that core maintenance competencies are honed, not lost.
For the acquisition community, these updates formally shift sustainment from a costly afterthought to a core design requirement. Program managers and the acquisition workforce now have the blueprint to integrate the product support analysis activities into the systems engineering process from the beginning, using analytical rigor to develop reliable designs and affordable support plans. This codifies an “own, not rent” philosophy, ensuring that systems fielded to the FMF are both highly capable and sustainable, which in turn builds a more resilient, self-sufficient force.
Arming the Acquisition Workforce: Empowering the Fleet
To turn policy into battlefield advantage, the Marine Corps is arming its acquisition workforce with the authority, tools, and analytical capabilities needed to execute the Secretary of War’s vision. This empowerment is being driven through three key lines of effort: restructuring leadership for integrated decision-making, providing tactical tools for smarter contracting, and embedding a data-driven mindset for sustainable systems. A cornerstone of this empowerment is how the Marine Corps is currently standing up a Portfolio Acquisition Executive for Marine Corps ground equipment. The Portfolio Acquisition Executive will be the single accountable commander for delivering warfighting lethality, moving beyond the simple management of program performance—breaking down the traditional, inefficient coordination between individual programs. This structure will empower the Portfolio Acquisition Executive to make rapid, integrated decisions that accelerate outcomes and provide a decisive edge, shifting the focus from managing programs to delivering a unified warfighting solution. For the FMF, this means receiving systems designed to work together from the start, creating a cohesive and far more lethal capability on the battlefield.
To complement this empowered leadership with practical tools for execution, Marine Corps Systems Command is also launching a dedicated site within its Logistics Knowledge Center. Previously, the workforce lacked streamlined access to the specific contractual language required to secure intellectual property and enforce sustainability goals. This new initiative solves that problem by providing a centralized repository of critical contracting language, data item descriptions, and additional toolkits and resources providing the tactical knowledge to write to write stronger contracts that secure data rights and break vendor lock where appropriate. The impact on the Marine in the field is direct: the technical data needed to repair their equipment will be available at the point of need, dramatically increasing self-sufficiency and reducing mission-crippling downtime.
The third piece of this empowerment strategy is embedding a data-driven mindset. To that end, Marine Corps Systems Command is further empowering the workforce with its updated Reliability-Centered Maintenance policy and handbook. The Marine Corps has traditionally relied on maintenance that is either reactive or based on fixed schedules, resulting in unnecessary work and unexpected equipment failures. Reliability-Centered Maintenance provides the data-driven analytical engine to create smarter product support strategies, determining the most efficient maintenance based on a system’s reliability and operating context. This policy is the catalyst for moving toward a predictive model using Condition-Based Maintenance Plus when the process determines the need for it on a particular system. For the acquisition workforce, Reliability-Centered Maintenance provides the analytical proof needed to build intelligent, affordable sustainment plans from day one. For the Marine, this translates to higher equipment availability and reliability, allowing maintainers to focus their efforts where they are most needed.
The Secretary of War’s mandate has set the clear, uncompromising direction: acquisition is warfighting.
This combination of empowered leadership, tactical tools, and analytical rigor is a force multiplier. The Portfolio Acquisition Executive provides the strategic why, the Logistics Knowledge Center delivers the contractual how, and the Reliability-Centered Maintenance policy provides the analytical proof. Together, these initiatives arm the workforce with the strategic authority, tactical precision, and data-driven justification needed to break down institutional barriers and deliver fully sustainable warfighting solutions. This ensures that the systems fielded to the fleet are not just collections of parts, but integrated, reliable capabilities designed to be owned and dominate in the battlespace, fulfilling the promise of a truly self-sufficient force.
Conclusion: Forging an Unfair Fight
It is this self-sufficiency that ultimately forges the unfair fight. The Secretary of War’s mandate has set the clear, uncompromising direction: acquisition is warfighting. Within the Marine Corps, this is an operational imperative. We must see our contracts as the first weapon sent downrange, engineered from the start to forge an unfair fight in our favor.
If the Marine Corps wants to win in austere conditions, we cannot merely field capabilities; we must be able to own it, repair it, sustain it, and fight with it indefinitely, even when the logistics tail is thin, contested, or cut entirely. That is how we preserve tempo, maintain lethality, and ensure the FMF remains truly expeditionary—not just in doctrine, but in execution.
Yet, for all the progress being made, we must recognize that the journey has just begun. The hard part starts now: the daily act of implementation, of changing a culture and holding ourselves accountable to these new standards. Success will not be measured by the documents we publish, but by the contracts we award, the data we secure, the deliverables we accept, and the speed, lethality, and self-sufficiency we deliver to the FMF.
The acquisition professionals of the Marine Corps are postured for this challenge, ready to prove—in the words of the Secretary of War—that in acquisition, just as in combat, “speed wins and speed dominates.”
ABOUT THE AUTHOR
>Mr. Bond is a prior Marine Corps Logistics and Intelligence Officer and the Product Support Director at Marine Corps Systems Command, where he has worked since 2010. He holds a Bachelor of Science in Computer Engineering from Embry-Riddle Aeronautical University.